DKMS
|
Size: 2009
Comment:
|
Size: 2428
Comment:
|
| Deletions are marked like this. | Additions are marked like this. |
| Line 1: | Line 1: |
| = DKMS do not work on systems with Secure Boot enabled = | = DKMS modules need to be configured to work with UEFI Secure Boot = |
| Line 4: | Line 5: |
| Because of those changes, DKMS modules will not work on systems with Secure Boot is enabled. | Because of those changes, DKMS modules will not work on systems with Secure Boot enabled unless correctly configured. |
| Line 6: | Line 7: |
| In order to make DKMS work, Secure Boot needs to be disabled. There are several methods to disable Secure Boot in your system: | In order to make DKMS work, Secure Boot signing keys for the system must be imported in the system firmware, otherwise Secure Boot needs to be disabled. There are several methods to configure your system to properly load DKMS modules with Secure Boot enabled. |
| Line 8: | Line 9: |
| == Method 1 - Disable Secure Boot from BIOS == | == Method 1 - Install the DKMS package you need == Simply install the package you need. Packages that make use of DKMS should prompt you to add new keys or disable Secure Boot, as appropriate for your system, and should do so automatically. == Method 2 - Disable Secure Boot from BIOS == |
| Line 14: | Line 19: |
| == Method 2 - Disable Secure Boot in shim-signed == | == Method 3 - Disable Secure Boot in shim-signed == |
| Line 32: | Line 37: |
| You can still enable Secure Boot in shim-signed again. Just execute '''sudo update-secureboot-policy --enable''' and then follow the steps above | You can still enable Secure Boot in shim-signed again. Just execute '''sudo update-secureboot-policy --enable''' and then follow the steps above. |
DKMS modules need to be configured to work with UEFI Secure Boot
Following an UOS approved spec, Ubuntu is checking module signing by default, on kernels 4.4.0-18.34, 4.4.0-21.37, 4.2.0-42.49, 3.19.0-65.73 and 3.13.0-92.139 onwards. You can read more details in this bug in Launchpad.
Because of those changes, DKMS modules will not work on systems with Secure Boot enabled unless correctly configured.
In order to make DKMS work, Secure Boot signing keys for the system must be imported in the system firmware, otherwise Secure Boot needs to be disabled. There are several methods to configure your system to properly load DKMS modules with Secure Boot enabled.
Method 1 - Install the DKMS package you need
Simply install the package you need. Packages that make use of DKMS should prompt you to add new keys or disable Secure Boot, as appropriate for your system, and should do so automatically.
Method 2 - Disable Secure Boot from BIOS
- Enter BIOS setup
- Disable secure boot
- Save configuration
- Reboot the system
Method 3 - Disable Secure Boot in shim-signed
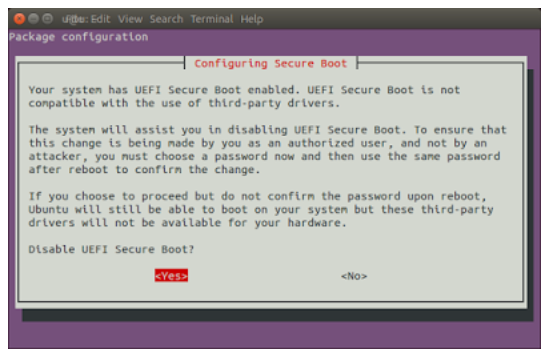
Open a terminal (Ctrl + Alt + T), and execute sudo update-secureboot-policy and then select Yes.
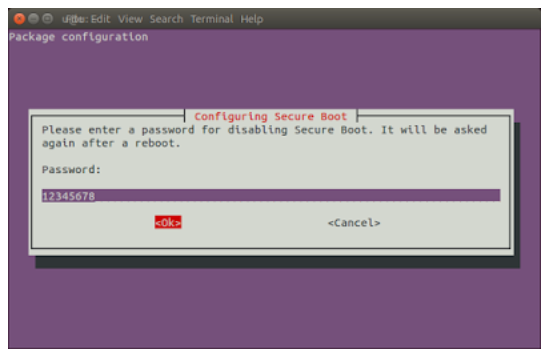
- Enter a temporary password between 8 to 16 digits. (For example, 12345678, we will use this password later
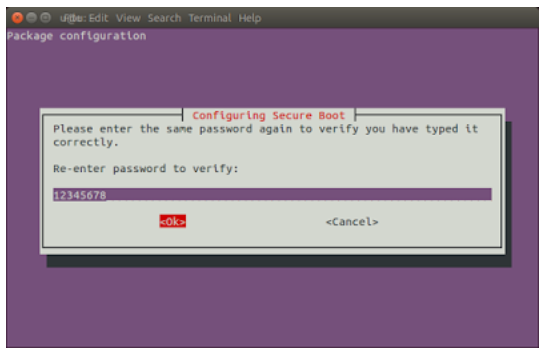
- Enter the same password again to confirm.
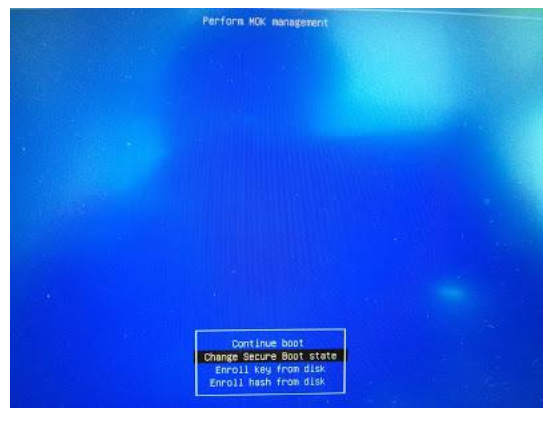
- Reboot the system and press any key when you see the blue screen (MOK management

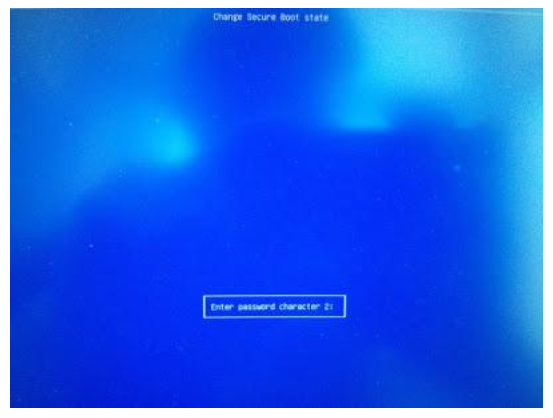
Select Change Secure Boot state
Enter the password you had selected in Step 2 and press Enter.
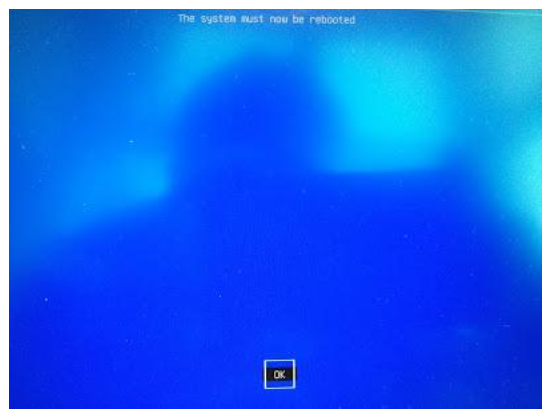
Select Yes to disable Secure Boot in shim-signed.

Press Enter key to finish the whole procedure.
You can still enable Secure Boot in shim-signed again. Just execute sudo update-secureboot-policy --enable and then follow the steps above.
UEFI/SecureBoot/DKMS (last edited 2018-06-26 19:53:49 by cyphermox)